Walk this Way, Talk this Way: Using Multiple Biometrics

Combining gait analysis, voice recognition and other biometric identifiers provides a fraud-resistant security solution

Major General (ret.) Aharon Zeevi Farkash, FST Biometrics
According to the statistics, terror attacks are continuing to climb as political climates heat up and radicals look for security weaknesses they can exploit to further their messages globally. The list of cities that have fallen victim to major attacks keeps growing: Tel Aviv, Istanbul, Nice, Brussels, Quebec City, Orlando, and more.
So what can be done to stem the tide of global terror? The answer begins with better intelligence.
The ultimate goal of intelligence would seem to be finding the one source of information – the one informer or spy – who could provide all the answers needed. But this is a fallacy. In the world of intelligence, the best way to get answers is by gathering information from multiple locations, an ecosystem of sensors that combine to provide a clear picture of a situation that security personnel can assess to prevent terror attacks.
This ecosystem can include a vast array of sources: signal intelligence, cyber intelligence, visual intelligence (from satellites, surveillance balloons, and drones), special forces, human intelligence, interrogations and others. Any of these sources alone would do little good; but when combined, they provide a clear picture of the security landscape.
The highest levels of military intelligence fuse all of this information together in real time and determine actionable intelligence for end users, namely, special forces and similar units.
This leaves us with a clear, sound approach to proactive intelligence and security, one that involves the fusion of sensors, stories, and information. This is a powerful thing in the intelligence world. Real-time data fusion is what allows agencies to approach security with a preventive philosophy that helps to prevent hostile events from occurring.
Global Megatrends and the Need for Convenient Security
There are two global megatrends that greatly affect the way in which we approach security. First is the growing need to prevent terrorism. Second is the increase in urbanization with the rise of megacities during the past several years. As a result of these two trends, proactive security has become a necessary part of our reality.
How can we protect ourselves – physically and technologically – from these real threats to our safety?
Security analysts, researchers and developers are coming to the conclusion that a strong, unified, multi-tiered biometric security solution is the next step in public and private protection.
But can developers create a technology that is accurate, private and convenient enough that people do not feel like they are living in a police state? In fact, the technology for such a solution is closer than one might think.
Why High-Level Security Is Not Enough
Alongside the security issues stands another challenge: a fast-paced, instant gratification generation that demands efficiency and convenience, as well as security. It is not enough to just have a solid security system in place. People want to feel unwavering protection, and they also want it to be instantaneous, seamless and easy. Imagine having to stand in a long line of shoppers because the identity verification software is slow. It is unlikely that consumers would tolerate such delays.
Many people are willing to forgo safety for convenience, adopting an attitude of, “I know it’s safer to do it that way, but I just can’t be bothered.” More often than not, for example, people would rather compromise the data on their phones by not using a PIN than give up slightly faster access to their Facebook app. Society would quickly dismiss a security system that takes too much time, is cumbersome, or is inconvenient to use.
A hack-resistant, flexible, full suit of armor that is also fast and easy to use? Are we demanding too much from technology? Maybe, but with the right minds set to the task, security system developers are rising to the challenge, and they may have come up with a solution.
Biometrics for Proactive Security
There are clear needs that must be addressed to meet the following demands:
- A solution that provides a high level of security, while not making people feel that they live in a police state
- A solution that is convenient for users and does not interrupt their pace of life
Biometric technology provides a solution. Biometrics allow us to quickly and securely identify individuals before they even enter a building. This can prevent many security breaches.
However, the question then becomes, what is the strongest, most effective and most convenient approach to preventive biometric security? The lessons from intelligence gathering apply to biometrics as well: what we need is fusion.
Any sensor on its own – facial recognition, fingerprints, iris recognition, voice recognition – cannot provide the accuracy, speed or aesthetics needed for strong security that is also convenient.
The strongest, most convenient and most secure forms of biometric technology employ a fusion of technologies to provide speed and accuracy, as well as simplicity, to the end user.
The most secure and convenient biometric identity verification technologies must leverage the power of fusion. For example, fusing face recognition and body behavior analytics, including height, gait and other characteristics, is very accurate and does not require a user to stop for identification. This fusion of sensors allows a user to understand a person’s identity in real time, with a high degree of accuracy and speed.
Single Mode Biometrics and Fraud Concerns
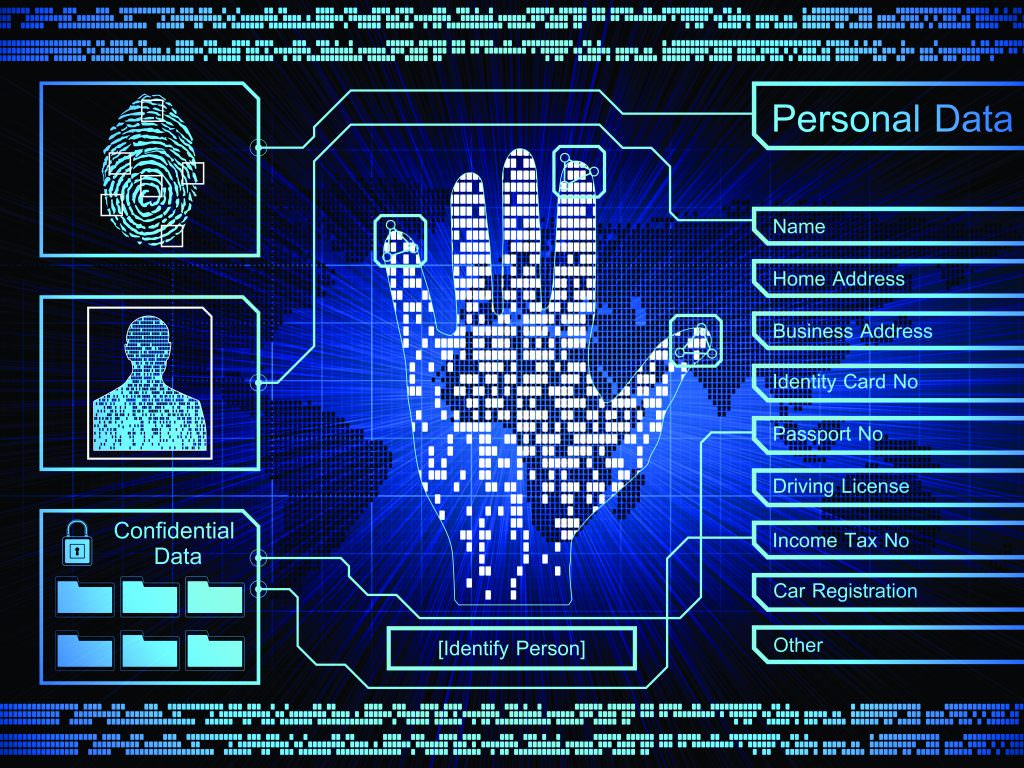
Biometrics are a powerful way to provide identity verification, and the range of biometric security options is vast and growing. Currently, the public can make use of fingerprint scanners, iris scanners, facial recognition, and gait analysis tools. Other technologies that are still in the research stage include ear scanners, speech pattern recorders, and heartbeat data monitors. Even typing style is being studied for possible future use.

On the surface, these may seem like sure-fire security and identity protectors – after all, how can someone possibly fake these intrinsic biological components? Yet, any technology, when it stands on its own, can be susceptible to fraud.
Identity theft is no longer just for cyber criminals who go online, steal credentials, and rack up bills on somebody else’s credit card. In fact, the term “identity theft” is taking on a more real definition than ever before. It is now being perpetrated at a biological level, with biometric factors being duplicated and stolen in new, almost surreal ways.

Fingerprints
Hackers are notorious for lifting fingerprints off of doorknobs, drinking glasses, receipts, and other publicly accessible items/areas. What’s even more disturbing than this is the recent discovery that a high-resolution image is all a talented criminal needs to create a duplicate of a person’s fingerprints.
Fingerprints can be duplicated using materials as rudimentary as Play-Doh or ink from a printer. Photocopies, printed circuit boards, silicone and rubber cement have also all been implicated in fingerprint copying. A simple piece of masking tape can even pick up a fingerprint for replication. Technology itself seems to be against the fingerprint scanner – a seemingly harmless glove has been developed, crafted to help smartphone users fight the cold by grafting the user’s fingerprints onto the glove.
Eye Scans
Faking an eye scan is easier than it looks. Using a high-resolution image, developers can make contact lenses that duplicate the shape and pattern of a person’s eyes. And these lenses are completely unnoticeable. A security guard will not be able to see that anything is amiss if a person walks in with this fraudulent eyewear.
Biometric Fusion: Ultimate Security, Ultimate Convenience
Fusion is not a new concept; it encompasses the idea that “the whole is greater than the sum of its parts.” The idea of biometric fusion is to combine the strengths of different technologies so that each one complements – and compensates for the shortcomings of – the other. In addition, fusion adds complexity to the identification, making biometric fusion almost impervious to fraud.
One of the most advanced biometric fusions available today includes facial recognition and body behavior analytics. What makes this combination so strong?
First, gait and body behavior biometrics, while newer to the market, are making a big impact because of their efficacy. Each person has a unique combination of movements. In fact, gait is probably one of the hardest biometric signatures to replicate. Even the most advanced robotics have not been able to successfully duplicate the movements and nuances of a human body. This makes gait and body behavior some of the strongest biometric guards available today.
Combining body behavior with facial recognition creates an extremely strong PAD (presentation attack detection) that is nearly impossible to crack. The likelihood of a fraudster being able to replicate a person’s face, while showing liveliness, and also copying exactly that person’s body characteristics, including height, gait, and specific behaviors, is vanishingly small.
It is not hard to see how a fused solution can help prevent fraud. Copying a fingerprint may be easy enough, but how successful would a criminal be at spoofing a system that scans a user’s face and gait? This is nearly impossible.
The Solution to a Growing Problem
By combining the strengths of multiple biometric markers – by building a complex fusion – we create a system that is stronger and more resilient than any one of the components could ever be by itself. And all of this is done without causing a negative impact on time and convenience.
While some solutions include multimodal biometrics (combining fingerprints and a PIN, for example), forward-looking industries are starting to adopt biometric fusion technologies to secure facilities, improve operational efficiencies, and provide better, more catered experiences to users. The revolutionary benefits of biometric fusion will soon be seen everywhere – from personal devices like smartphones, laptops, and banking apps, to public areas such as stadiums, hospitals, airports and universities.
All of these systems give us a clear picture of how combining multiple biometrics can combat threats. Even the best hacker would be hard-pressed to duplicate a person’s face, gait, movements and voice. Fusion takes strength in numbers to a whole new level, and keeps attackers at bay.
Maj. Gen. (ret.) Aharon Zeevi Farkash (farkash@fstbm.com) is founder and president of FST Biometrics (www.fstbm.com) and was head of the Israeli Defense Forces Directorate of Military Intelligence from 2002 to 2006.
