The Not So Friendly Skies

Drones represent a rapidly growing and evolving threat

Nathan Ruff, Coalition of UAS Professionals
Unmanned aircraft systems (UAS), better known as drones, are making headlines frequently.
Drones drop grenades on Coalition Forces.
Drones land radioactive material on the roof of the Japanese prime minister’s home.
Drones steal industrial trade secrets by hovering outside a 30th-floor window while spoofing a printer’s MAC address.
And the list is only getting longer and more troubling.
To be specific, the drones in the above instances are officially denominated as sUAS (small unmanned aircraft systems). These are not the large, military-grade MQ-1 Predators or MQ-9 Reapers carrying 800-pound munition payloads. Rather, this class of drone is defined as weighing less than 55 pounds “wet,” which includes all peripherals. The classification includes rotorcraft, fixed wing and hybrid varietals, each with its own specific strengths and weaknesses.
For example, if the goal is to deliver contraband to someone inside a prison’s walls, a rotorcraft, given its ability to hover precisely, small noise signature, and capability to be operated from miles away, would likely be the preferred choice. If, however, speed, distance and the ability to carry heavier payloads were priorities, than a fixed-wing drone would be a better alternative. The options are many, which makes defending against the threat more challenging.
To further complicate the situation, drones are popping up everywhere. The FAA estimates that 2.5 million drones were sold in the United States in 2016, and the agency projects that, by 2020, more than 7 million drones will be operating in the national airspace. Remote controlled aircraft have been around since World War I, but it has only been in the past 12-18 months that this rapid growth has occurred. Although component miniaturization, advances in batteries, and accelerated processing power were required for this technology to go mainstream, what has really driven the drone phenomenon is GPS stabilization.
In the past, piloting a remote controlled aircraft took considerable skill and practice. That is no longer the case.
Mastering the skills required to fly a drone over a prison wall, or position it 400 feet above the ground to snap photos of a secure facility, takes only about 15 minutes of practice. In fact, it usually takes longer to get the drone out of its packaging than it does to learn to fly it competently.

All of this has led to the proliferation of these advanced airborne robots at a price point at which they can be disposable items. Need a drone that is capable of spying on a neighbor or delivering a chemical agent? For around $400-$500, you are ready to start flying. And since drones are not required by law to be registered or to have any identification markings, they can be abandoned with little concern after completing their nefarious missions.
Defenses and Regulations
So how great a risk do drones pose to the modern security professional? As usual, the answer depends on the specifics of the situation. For some, drones will merely represent a nuisance with no real operational implications. For others, the potential threat is much more significant.The former is best classified as a dumb actor scenario – someone flying a drone with no respect for privacy, nor a clear understanding of regulations, local ordinances, and safe operating protocols. This type of intrusion is best handled by enhanced awareness. A counter-UAS system will alert security of the incursion, triangulate the offender’s location, and facilitate a response. Should that not work, local law enforcement can be called based on traditional statues such as trespass, reckless endangerment, and invasion of privacy.

On the other end of the spectrum is the bad actor scenario. This is when someone is using a UAS to gather confidential information or to create a threat to life or property. Because the UAS industry is nascent, regulations are lagging. Outside of the U.S. military, there is currently no legal way to actively neutralize a drone threat. UASs are technically unmanned aircraft, and it is illegal to shoot down, disable or interfere with the flight of any aircraft in the national airspace. Thus, physical interdiction is off the table. Furthermore, jamming, hacking, spoofing, or actively taking command of the drone by interrupting its radio frequency crosses a Federal Communications Commission (FCC) line and is also illegal.
The Federal Aviation Administration (FAA) controls the airspace, but it is not equipped to police the skies. Fines and revoked credentials are the limited tools they wield, and they do not have the manpower to identify most perpetrators. It is not a surprise, then, that the private sector has begun to fill the gap with myriad counter-UAS solutions. Rayguns (directed energy emitters), jammers, spoofers, predator drones, nets, and even trained birds of prey are just a few of the options making their way to the market. These technologies may be the future, but without the ability to deploy them legally, no security practitioner should consider such a purchase unless there is an operating agreement in place with a governmental agency. Outside the United States, there is a much more conducive environment for active countermeasures. All of this poses a major conundrum for anyone needing to defend against a bad actor scenario.

Numerous interagency working groups and task forces have been formed to figure out a regulatory solution, but it will take time.
Regulations regarding both flights over people and micro-UASs have stalled because of concerns raised by the Department of Justice, the Department of Homeland Security, the FBI, the intelligence community, and law enforcement about how to identify drones in the air. Their argument is that, without the ability to track UASs, understand who is operating them, and have in place a mechanism for accountability, drones should not be flying over people. The latest estimate for when a rule could be released for flights over people is May 2018.
There are many technological solutions to these challenges in the works, but, again, the process of testing, legalizing and implementing them is not fast. One good way to start sorting out “good actors” from “bad actors” today is to simply require UAS pilots to file a flight plan similar to how manned aviation has operated for more than a century. Submitting an unmanned operating area (UOA) notice takes about 30 seconds to accomplish, provides critical information regarding the altitude and timing of operations, and is a great way to improve the situational awareness of not only other UAS pilots but the entire manned aviation community, as well. One app, for example, allows users to easily file UOAs from a phone or tablet, and the notification is instantly visible in the flight briefing system that 80,000 manned aircraft pilots use each week. Obviously, a “bad actor” would not use the system, but, by understanding who is playing by the rules, identification of rogue flights becomes a much more transparent process. This, coupled with ADS-B or SIM card technology that has become small enough to be viable on drones would allow everyone operating in the national airspace to both “see” and “understand” the intentions of drones in flight.
Threat Vectors
Until the day comes when all drone flights are conspicuous, it is crucial that security professionals understand the potential threat vectors a drone could leverage and implement measures to deter such intrusions. Understanding how UASs can be used maliciously will enable security practitioners to think through this new class of vulnerability and facilitate the creation of a strategic defense. Delivery threats (both physical perils and contraband delivery) and intelligence gathering represent two main areas of susceptibility for the security industry.

In terms of delivery threats, the ability to put a 9mm firearm on a drone and operate it remotely with a disturbing degree of accuracy was proven by an 18-year-old in Clinton, Conn., in 2015 in a viral video. The exhibition, though, also highlighted an important limitation, in that firing a percussive weapon from a UAS platform creates substantial kickback, resulting in temporary destabilization. Although multiple shots were fired, this was effectively a “one-and-done” threat with regard to most real-world situations. However, a recoil suppression gimbal is now available that allows a sniper rifle to be mounted on a UAS platform and fired multiple times with a high degree of accuracy.
Because it is common practice for agricultural drones to spray crops, the potential to use a drone to disperse dangerous biologic agents is obviously a concern. The ability to fly a drone into a population center and drop microorganisms from above depends only on access to the bioweapon; the delivery vehicle is readily available and its purchase is unregulated. ISIS uses drones to drop modified grenades, but this is a rudimentary first step. Microscale reactive ordnance as a payload represents a more significant threat given its “weight-to-bang” ratio. Thinking a little bit more creatively, mounting a thermal breaching tool on a drone platform presents additional threats. The flashlight-sized device can cut through a half-inch steel bar in less than a second while burning at 5,000 degrees Fahrenheit.
“Swarming” represents a particularly unsettling delivery threat. The potential for UASs to be leveraged as asymmetrical warfare tools has already been discussed, but extending that concept to a swarm of drones operating with a common objective and controlled by a single pilot poses the exponentially greater risk. One drone can do damage, but imagine 500 drones operating in concert: a minefield in the sky that cannot be skirted or easily neutralized. Combining this concept with autonomous operations and some degree of artificial intelligence, one can start to imagine a formidable future threat. A drone swarm could comprise “bombers” and “specialists,” similar to the division of labor found in an ant colony. Specialist drones could be tasked with mapping any new environment the swarm enters with simultaneous localization and mapping (SLAM) technology, assessing/overcoming threats, capturing intel, etc., while the majority of the swarm is equipped to drop ordnance or simply launch kamikaze attacks into designated targets. At this point in time, UASs flying in cooperation can create networks, transfer information, make deliveries, or even “dance” (as demonstrated during the 2017 Super Bowl halftime show).
Swarms of killer drones may seem like science fiction, but the technology required to make them a reality exists today.
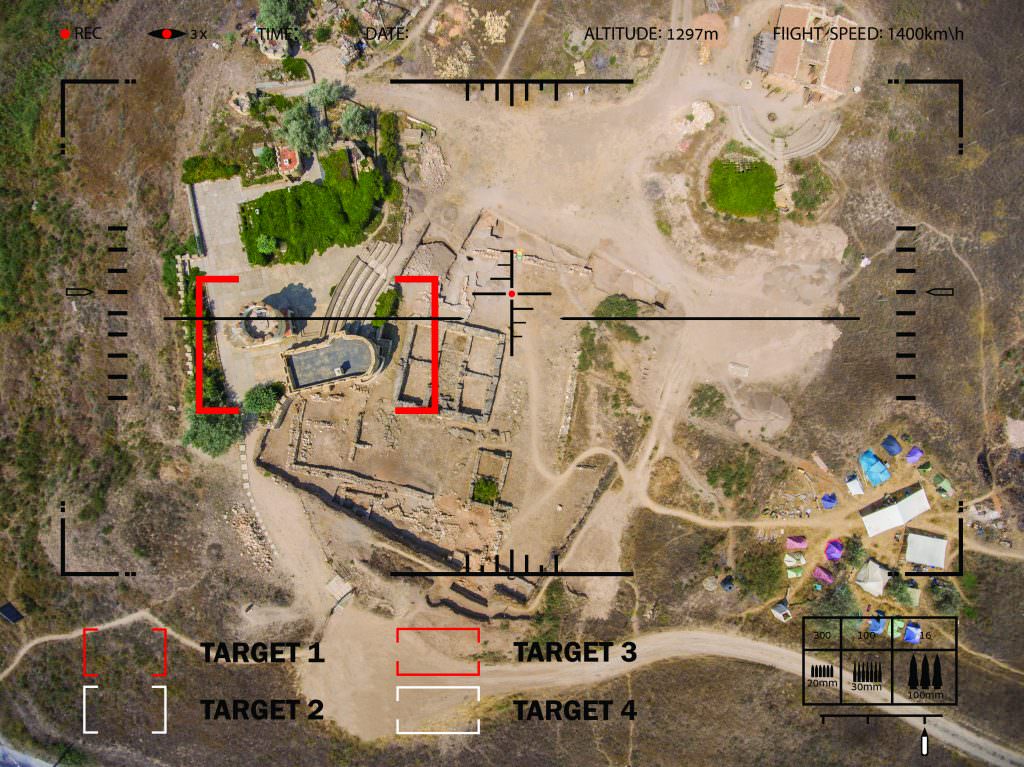
Gathering intelligence is the second main area where UASs have proven to be a disruptive technology. PwC estimates that drones represent a $127 billion global market, and the Association for Unmanned Vehicle Systems International (AUVSI) projects the creation of 70,000 new jobs in the sector in the United States over the next three years alone. One of the reasons behind this growth is that collecting information from above historically required a helicopter, fixed wing airplane or satellite, so the savings that UAS technology provides are huge. To complement these new aerial platforms, sophisticated sensor packages are available off the shelf that provides thermal imaging, 6K video, or 50-megapixel stills. In addition, magnetometers, facial recognition, and airborne chemical analysis are other areas where drones could potentially perform better than current solutions.
Capturing meaningful data from above is no longer a complicated operation; it is big business.
So what does the near-term future hold for this rapidly evolving technology? The likely answer is automation and integration.

Automation and Integration
Fully autonomous flight is the future: UASs capable of flying missions without a person at the controls. This already exists to some extent, and advances in machine vision and machine learning (artificial intelligence) have been truly impressive. Not only can drones “see” obstacles in their path, they have the onboard processing power to make adjustments so that the sortie can be completed.
Soon, humans will set the objectives, and airborne unmanned robots will execute the mission.
UAS integration into the Internet of Things is happening now. Taking the concept of automation to the next level, consider the type of information that will become available if every drone flight is not only performing its intended assignment but is also simultaneously capturing and sharing information about its environment. This can include, say, real-time pictures of traffic conditions, weather, or crop growth. Or, more troublingly, what time your car is parked in front of your home, when you go for a jog, or who visits your house. The U.S. Army recently banned drones from a Chinese manufacturer because of the potential to covertly record and transmit information back to that country.
Autonomous vehicles and autonomous drones are traveling on a parallel path. In fact, since the technology is analogous, a number of manufacturers are investing in both markets. The idea is that autonomous vehicles will need to have an up-to-the-millisecond picture of roadways in order to operate safely. Thus, if a box falls off a truck on the highway, the first vehicle behind it feeds that new information into the global database so that all other vehicles headed in that direction are aware of the potential hazard. Drones represent one more node of data collection to feed into this master picture.
It is clear that drones are a new and rapidly developing threat vector. The technology also represents a sea change for security services desiring to integrate drones into their portfolio of solutions. The ways that drones can be used to compromise security seem limited only by the imagination, so the ability to counter these new threats will require thinking beyond traditional approaches. Devoting the time and effort to assess how exposed assets are to this type of peril and, if necessary, crafting an interdiction strategy is an exercise well worth undertaking.
Nathan Ruff (nathanruff1@gmail.com) is the executive director of the Coalition of UAS Professionals (www.uascoalition.org). He also manages NKR Partners Consulting Group (www.nkrpartners.com).
