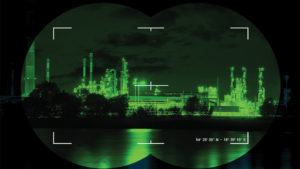
24-Hour Perimeter Protection

Relentless defense for critical infrastructure
The challenges to perimeter protection seem to grow more nefarious every day. The bad news is that intruders are increasingly inventive and unscrupulous. The good news is that the security operators are leveraging more innovative technologies to mitigate and deter these threats.
Effective perimeter protection on a 24/7 basis is a crucial part of the defense of critical infrastructure – the assets, networks and systems, either virtual or physical, that are so vital to security and safety.
The Challenges
Over the past few years, securing the nation’s critical infrastructure has become a top priority. Security has arguably become the most important aspect of any airport, seaport or utility’s business. Operations managers must continually answer the question, “Are we protected?”
The common concerns involve a combination of factors:
- Physical plants cover enormous areas, with many points of entry and extended perimeters, often in remote areas that make monitoring difficult.
- Campuses contain complex, highly restricted and expensive equipment where proper access and use must be controlled.
- Facilities such as airports have areas with varying levels of access authorization, from the check-in area to the airline gate to the baggage claim.
- Operations at these locations take place 24 hours a day in heat, rain, sunshine or darkness.
When designing an effective solution to secure the perimeter, there is no one-size-fits-all solution, primarily because no two perimeters are the same. Terrain, climate and threat profile all affect the decisions of what technologies are required for the best solution. Typical choices include patrolling personnel, fences, walls and/or trenches, unattended ground sensors, unmanned aerial sensors, radars and thermal imaging.
Even with this variation, the technologies that are being increasingly deployed in the critical infrastructure sector for intrusion detection are radar, thermal imaging and multisensor cameras, which are controlled through advanced Physical Security Information Management (PSIM) solutions. Combining technologies to create solutions with multiple complimentary capabilities, like combining radar with mobile cameras, or high-definition surveillance cameras with thermal imaging technologies, results in an overall system that is greater than the sum of its individual parts.
Radar
 As always, understanding the nature of a threat is key to intercepting and defeating it. Fixed, mobile or trailer-based, the latest ground surveillance radar systems can detect and track multiple threats simultaneously, even beyond perimeter lines. This enables security personnel to monitor and control their security zone by intercepting threats early, before they have had opportunity to complete their mission. Today’s ground surveillance radars are also exceptionally fast in terms of target detection and acquisition.
As always, understanding the nature of a threat is key to intercepting and defeating it. Fixed, mobile or trailer-based, the latest ground surveillance radar systems can detect and track multiple threats simultaneously, even beyond perimeter lines. This enables security personnel to monitor and control their security zone by intercepting threats early, before they have had opportunity to complete their mission. Today’s ground surveillance radars are also exceptionally fast in terms of target detection and acquisition.
In maritime search and rescue operations, as an example, improved radar surveillance can work together with infrared thermal imaging to cover a wider area and interpret images quickly so that crews can rapidly decide whether to continue the search pattern or investigate a target.
Airborne systems operate on helicopters, fixed-wing aircraft, ships, land vehicles and observation towers around the world. In a time when threats are varied, systems must be as flexible as possible to adapt quickly to challenges.
In fact, the most effective border surveillance systems combine performance, coverage and reliability to create the most efficient solutions on the market today for border protection, coastal surveillance, vessel traffic monitoring, airport security and other large perimeter security applications.
Effective radar detects threats over great distances, providing important reaction time. In addition, it is virtually impossible for targets to advance without detection, including slow-moving targets. Radar provides important targeting parameters, including range, bearing, course, speed and GPS coordinates.
Dual-Sensor Thermal Imaging
 Detecting a potential threat, of course, is just the first step. Once an object is detected, it must be identified and its threat level determined. Without clear, long-range visual analysis of detected threats – on land or on water – operators are unable to discern the difference between false alarms and alerts that require some sort of action.
Detecting a potential threat, of course, is just the first step. Once an object is detected, it must be identified and its threat level determined. Without clear, long-range visual analysis of detected threats – on land or on water – operators are unable to discern the difference between false alarms and alerts that require some sort of action.
Effective long-range dual sensor thermal imaging combines thermal and high-definition visible-light imaging sensors that easily network with other sensors, as well as with command and control software. Although many believe that thermal imaging is only effective at night, thermal imagers equipped with powerful zoom optics often outperform their visible-light counterparts. These systems can provide such reliable threat detection at ranges so extreme that they’re limited more by topography than by the energetic limits of the sensors themselves.
Multi-sensor cameras are an extremely versatile solution for critical infrastructure protection in total darkness, bright sun and/or adverse conditions. The best are equipped with a continuous optical zoom lens for superior image quality, and are designed for system integration.
 Additionally, thermal cameras are ideal for video analytics. Visible light cameras can be easily fooled by many naturally occurring phenomena, such as blowing trees, shadows, insects, birds or oncoming cars. In terms of motion detection, microwave, fence sensors, motion sensors, and radar can all detect a possible intrusion, but they are essentially “blind” technologies compared to thermal imaging. When a motion sensor is triggered, a user still needs an additional method of assessing the nature of the alarm, to determine the most appropriate response. For example, is it a person climbing the fence or just a harmless squirrel?
Additionally, thermal cameras are ideal for video analytics. Visible light cameras can be easily fooled by many naturally occurring phenomena, such as blowing trees, shadows, insects, birds or oncoming cars. In terms of motion detection, microwave, fence sensors, motion sensors, and radar can all detect a possible intrusion, but they are essentially “blind” technologies compared to thermal imaging. When a motion sensor is triggered, a user still needs an additional method of assessing the nature of the alarm, to determine the most appropriate response. For example, is it a person climbing the fence or just a harmless squirrel?
Because of thermal security cameras’ high-contrast video output, security professionals have found that they work very well with video analytics that are capable of classifying humans and vehicles, which is an obvious important factor when determining the correct response. They can provide more reliable alarming with fewer false reports than visible-light cameras, even during the day. Thermal imaging security cameras offer both alarming capabilities and reliable images – two solutions in one.
Command and Control Software
The command and control software is the brain of the overall system, the link that enables integration of all the elements. As such, it is important that this element provides security and surveillance in a high customizable, user-friendly environment. The best command and control systems can control virtually any number and combination of disparate devices with point-and-click simplicity.
The value of command and control software is that it seamlessly integrates all elements – cameras, displays, analytics, radars, fence detection, unattended ground sensors and other devices – from multiple manufacturers on multiple sites. This capability supports existing legacy devices as well as allowing systems to add new technologies. It provides unparalleled situational awareness from one control room.
 One defining feature of PSIM platforms is their scalability, accommodating the addition of servers and clients as needed. The benefit of having an intuitive and configurable client interface is that it provides operators with access to external monitors and monitor walls through simple drag-and-drop actions. The server environment is powerful enough to provide such features as device prioritization, system security and granular permissions control, alarm management, archived video storage and retrieval.
One defining feature of PSIM platforms is their scalability, accommodating the addition of servers and clients as needed. The benefit of having an intuitive and configurable client interface is that it provides operators with access to external monitors and monitor walls through simple drag-and-drop actions. The server environment is powerful enough to provide such features as device prioritization, system security and granular permissions control, alarm management, archived video storage and retrieval.
Among the additional tactical features a robust command and control software system should offer:
- Automated camera tracking: As intruders monitored by radars pass into defined detection zones, visible/infrared cameras are triggered to track and identify the moving objects.
- Radar support: The capability to overlap multiple radars will provide a detection area of virtually unlimited size.
- Infrared imagery: The capability to slew thermal cameras to follow moving objects in the dark. Users can toggle between infrared and visible imagery while viewing infrared video.
- Total position awareness: The capability to snap cameras and radars to their real coordinates on GPS-aligned maps, monitoring real-time positioning of radar tracks and GPS-enabled mobile resources.
- Advanced controls: The system should control advanced camera features used in perimeter surveillance such as range finders, trackers, and the ability to control all camera parameters.
- External display control: The platform should provide users with seamless control of monitor walls using sharing and collaboration features accessed through simple drag-and-drop actions.
- Scalability: The platform should support scalability by the capability of adding servers and clients as needed.
- Workspace configurability: Client applications should support the ability to create the most efficient layouts for the mission. Allowing multiple panes for maps, event lists, live and archive video, as well as enabling cooperation between these components, creates a truly “intelligent” user interface.
- Operator security: System security should be controlled by operator passwords, priorities and access privileges, as well as by controlling access to features and devices independently.
The Future of Perimeter Protection
As we’ve seen, the technology of safety and surveillance, especially as it applies to perimeter protection, will continue to evolve. What else will soon be seen?
Watch for these systems coming to your security zone soon:
- Aerial surveillance: The use of personal drones will only increase, especially now that the Personal Reconnaissance System (PRS) is now pocket-sized. This game-changing technology provides immediate situational awareness at a safe distance. In the civilian sector, they’re particularly useful in search and rescue missions, firefighting and law enforcement applications.
- Advanced biometrics: Go beyond traditional ink fingerprinting for identification with such solutions as an optical fingerprint scanner, an iris scanner, and a palm print scanner.
- Connected technology: The emergence of place-specific solutions that range from Internet and communication systems to document imaging, archival security and document sharing services.
- Perimeter patrol robots: They’re already entering the market.
Any business that wants to achieve the maximum level of security and protection of their intellectual and physical property should consider deploying these cutting-edge technologies, along with thermal imaging and radar systems.
John Distelzweig is general manager of FLIR Systems Inc.
