Good-Better-Best: Comprehensive Best Practices for Implementing Public Transportation Security Systems (Vol. 2)

Public transportation systems provide reliable access and affordable passage for large volumes of commuters. These systems are designed to reduce friction, allowing passengers to enter and exit seamlessly and on demand. This volume of people and ease of access, combined with the confined spaces and location of these systems in massive city centers, makes public transportation susceptible to adversarial targeting and threats. Adversarial targeting, such as terrorism, is indeed the worst case, but in systems like these, the day-to-day security and safety concerns are the ones that keep security teams busy. With so many vehicles and passengers in motion, accidents and incidents occur numerous times per day, and coordination with law enforcement is key.
In this guide for security practitioners – third in a series of Good-Better-Best (G-B-B) use cases – the Security Industry Association (SIA) provides comprehensive best practices for implementing security systems in public transportation environments, this time on the security operations centers and in-vehicle aspects of the market. This report is recommended to be used in tandem with the original volume, Good-Better-Best: Comprehensive Best Practices for Implementing Public Transportation Security Systems (Vol. 1).
- Executive Summary
- G-B-B: Public Transportation Volume 2
- Intelligent Security Operations Centers
- Security on Board Transportation Vehicles
- G-B-B Project Value Detail
Executive Summary
Whether you are a facility manager, risk management professional or safety officer or have more of a “traditional” title of security program manager, points of reference are an absolute must when investing capital in electronic security and safety solutions. The question remains, “What are the reference criteria needed to make an informed decision on the most appropriate offer of products and services for my facility?”
The fact that you have taken the time to actually research how to make an informed decision is a significant leap in the right direction away from “lowest qualified price” criteria; however, that does not mean understanding pricing strategy is any less important to measuring the improvement of a “Better” or “Best” from a minimum needs level that we’ll refer to as “Good” in this document. In fact, we will tackle pricing strategy and industry pricing considerations first in the body of this work in the section “Building the G-B-B Program – Price-Wise.”
Regardless of what offering is made and what criteria were used in developing that design, all choices need to reflect how the security dealer or systems integrator works together with the end user as a trusted advisor or business partner.
Good:
- Meets minimum compliance requirements
- Has security functions for most common threats
- Is capable of upgrade
Better:
- Provides better sensors
- Has functionality matching the customer’s operation
- Has basic systems integration
Best:
-
- Demonstrates measurable return on investment through technology enhancements
- Allows all systems to share data sets, enabling rich analytics
- Increases confidence level of situational intelligence through artificial intelligence and machine learning-based analytics
Good-Better-Best: Public Transportation Volume 2
Public transportation systems provide reliable access and affordable passage for large volumes of commuters. These systems are designed to reduce friction, allowing passengers to enter and exit seamlessly and on demand. This volume of people and ease of access, combined with the confined spaces and location of these systems in massive city centers, makes public transportation susceptible to adversarial targeting and threats. Adversarial targeting, such as terrorism, is indeed the worst case, but in systems like these, the day-to-day security and safety concerns are the ones that keep security teams busy. With so many vehicles and passengers in motion, accidents and incidents occur numerous times per day, and coordination with law enforcement is key.
For the third in a series of Good-Better-Best use cases, SIA focused on public transportation again – this time on the security operations centers and in-vehicle aspects of the market. SIA collaborated with industry professionals to outline Good-Better-Best security cases. SIA’s Public Safety Working Group, which brings together various stakeholders in the public safety ecosystem – including practitioners, integrators and manufacturers – then reviewed the guidance. This report is recommended to be used in tandem with the original volume, Good-Better-Best: Comprehensive Best Practices for Implementing Public Transportation Security Systems (Vol. 1).
According to guidance issued by the Federal Transit Administration, public transportation agencies should be moving from governance focused on compliance to a more proactive, data-driven program based on the principles of safety management systems (SMS). SMS helps organizations improve upon their safety performance by supporting the institutionalization of beliefs, practices and procedures for identifying, mitigating and monitoring safety risks. SMS activities proactively detect safety concerns and organizational factors and correct them using data-driven prioritization. As such, important to SMS’ success are:
- Effective collection, analysis and sharing of safety data
- Active, accurate and routine safety performance measurement
The Good-Better-Best approach matches this approach; as a system moves from good to best, the amount of data distribution and collection between systems increases. For example, sharing of data from security and safety systems with other transportation operational teams can help identify risks such as litter on the tracks, which can lead to fires, corroded or otherwise damaged rails or a person falling onto the tracks.
The Good-Better-Best approach matches this approach perfectly; as a system moves from Good to Best, the amount of data distribution and collection between systems increases. For example, sharing of data from security and safety systems with other transportation operational teams can help identify risks, such as litter in the tracks, which can lead to fires; corroded or otherwise damaged rails; and structural damage such as water leaks, which can lead to safety hazards to passengers.
The guidance in this G-B-B document considers security features to help mitigate the risk or aid in the resolution of incidents such as, but not limited to:
- Passenger misconduct, including violence
- Vehicular accidents
- Pedestrian accidents
- Tort incidents
- Acts of terrorism
Intelligent Security Operations Centers
The brains of the entire security operation of the transportation system are located in the intelligent security operations center. A security operations center should perform three functions:
- Aggregation of data from a variety of sensors located throughout the transportation system
- Analysis of data using computer-aided analytics and human analysis
- Having the tools to facilitate response based on the analysis of data – including communication to stations, transportation personnel and local first responders and law enforcement
The more robust the data set and analysis are, the more informed the response can be. A good transportation security operations center is fitted with systems that adequately collect data and can escalate security events to decision makers. Better systems increase the level of situational intelligence through the connection of data between systems and automatically correlate data from one system to another. For example, abnormal data from a motion sensor, along with live video from cameras deployed throughout the system, gives responders a clearer understanding of any situation that requires attention. When a system can combine this type of system data interoperability with data from external systems such as geolocation, social media monitoring and shared information from local law enforcement, solutions can deliver better and better situational intelligence from accurate analysis of these diverse data sets. While generally more data is better, it is the ability of the system to define and present an analysis of the correct data that determines success. Responders presented with unnecessary information can be just as ill prepared to respond as responders who are underinformed.
Mobility is synonymous with transportation, and the security and safety decisions that originate in the security operations center must be able to make their way to a mobile response team. In the better systems, mobile responders should be able to easily share information with other response teams. Part of response also becomes informing citizens using the transportation system of incidents and ways to avoid danger or delays that may arise from response. Rider and customer mobile applications that are tied to selected data from the security operations center allow for bidirectional communication between security and safety teams and riders helping to convey system status updates, providing confidence in the overall value of the transportation system for riders.
Security on Board Transportation Vehicles
In transportation systems nationwide, most vehicles are equipped with communication equipment that actively and passively transmit information to the intelligent communications center. No matter the transmission mechanism – radio, cellular, LTE or in some cases Wi-Fi –communications from the vehicle to the operations center must be on a secure network that cannot be co-opted by unauthorized users.
Onboard communications equipment can be driver controlled, operations center controlled or automatic. Technology such as GPS or automatic vehicle locators (AVLs), either included within or separate from mobile data terminals, provides real-time positional data for vehicles at all times. Emergency buttons for operators or passengers let operators (and the control center) know if there is an incident on the vehicle and also allow drivers to send covert distress alerts to the operations center.
While these types of communications have been on board transportation vehicles for quite a while, these communications technologies, when layered with other security sensors such as onboard video and audio focused on activity inside the vehicle and outside, give the transportation security center the data necessary to proactively and reactively provide incident response. Video combined with geolocation services can address situational intelligence questions such as:
- How many people are involved in the incident?
- Is the operator in control of the vehicle?
- Where did the incident start, and has it ended?
- Have any subjects left the vehicle? What direction did they go?
- What can passengers do in response? How can we get that message to them quickly?
The selection of technology within these transportation systems can improve value to the entire ecosystem of transportation stakeholders. In a system with communication, location, video, mobile and display technologies:
- The operator is assured greater safety along routes and given the tools necessary to help passengers during incidents.
- The passenger can take solace that activities on the bus are monitored and that they are given agency to report issues and can receive instructions on in vehicle displays or their own mobile devices.
- Incident responders can pull up live video, communicate to assailants and passengers and intervene with greater understanding of the entire situation.
- System maintenance officials can monitor network health in real time and update routes in real time.
Cybersecurity Within Connected Security Networks
Nationwide, public transportation vehicles share cybersecurity vulnerabilities. Concerns related to connected devices include unauthorized access, wireless network attacks and tampering with connected onboard systems to enable management, monitoring and communication. Beyond traditional physical security concerns in transportation, such as safety related to traffic, passengers, pedestrians and others road hazards, physical security and public safety dangers in include vehicles, particular buses being weaponized to breach restricted spaces, checkpoints and barriers. The confluence of physical and cybersecurity as systems evolve technologically and the growing prevalence of connected vehicles and the future of autonomous travel make cybersecurity increasingly vital to public safety.
On a bus, solutions to protect control of the vehicle itself might include the securing of vehicle diagnostic ports, sensors and signals. For protection of passenger, operator and control privacy, encrypting surveillance, communication and location data is critical. Connected infrastructure vulnerability mitigations include separating and securing onboard public and private Wi-Fi. Cybersecurity auditing of individual systems upon procurement can limit exposure to a host of cyberattack risks when these systems begin sharing data.
Public Health Mitigation
In the age of the COVID-19 pandemic and in the wake of evolving public health guidance, transit agencies have swiftly developed efforts to mitigate both passenger and operator risk, such as:
- Limiting onboard passenger capacities depending on vehicle type, including physical separations between the operator and passengers
- Adding entry/egress alternatives for passengers
- Emphasizing face covering requirements for passengers by making them available to those who may not be in compliance
Sanitizing and disinfecting vehicles and facilities is also a standard daily practice, prioritized for high-touch surfaces and high-activity locations. Security technology, including mask detection and traffic flow analytics, provides operations teams with a useful tool in pandemic-era rider management.
G-B-B Project Value Detail
In the G-B-B project value detail (spreadsheet), location symbols used are as follows:
- Numbered symbols indicate physical locations: ① ② ③ ④ ⑤ ⑥
The following are the G-B-B equipment details for each location, with a summary differentiating Good, Better and Best versions.
Demonstration of how ESS devices function are organized at a location, including video intercom, electric locks, video surveillance cameras and card readers/biometrics. To view the guidance with all graphs and charts, please download the full PDF.
① Security Operations Center
The security operations center is a centralized facility where the transit authority connects with their mobile fleet as well as related public safety agencies to analyze and monitor security-related operations, incidents and crises.
- Entry/exit card readers for access control and electronic audit trail, synchronized with video surveillance system cameras (All)
- Audio and video intercoms that are voice over IP (VoIP) compatible and video intercom that is video over IP compatible (desktop VoIP station) and mobile device compatible
- Physical barriers/intrusion detection
- Visitor management
- Key management
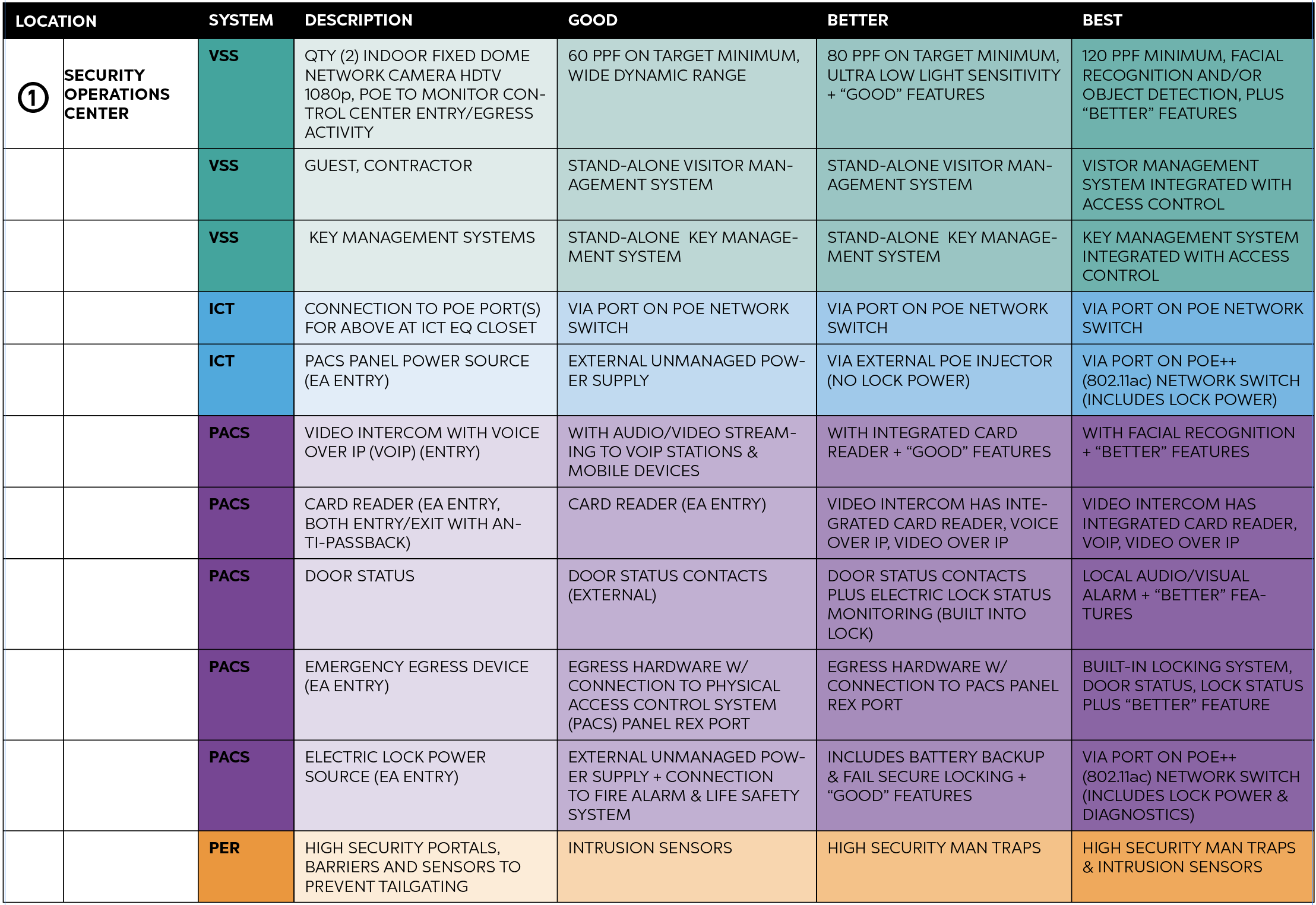
Good, Better and Best system recommendations for security operations centers, including specifications for video surveillance, ICT, PACS and perimeter systems. To view the guidance with all graphs and charts, please download the full PDF.
② Onboard Bus Surveillance
Onboard video surveillance cameras function to enhance passenger and driver safety. Cameras also work as deterrents to inappropriate behavior and can supply valuable evidence during investigations.
- Public address systems
- Passenger emergency call devices
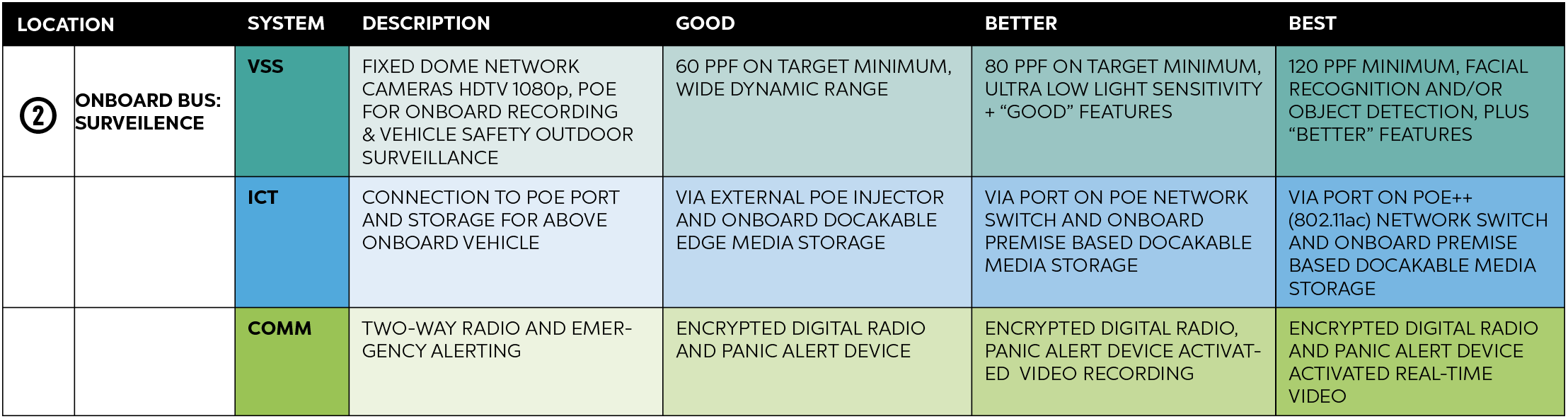
Good, Better and Best system recommendations for onboard bus surveillance, including specifications for video surveillance, ICT and communications. To view the guidance with all graphs and charts, please download the full PDF.
③ Bus Stop Locations: Communications
Bus stop locations offering communication devices, such as passenger assistance call devices, provide valuable features for passenger safety.
- Public address systems
- Passenger emergency call devices
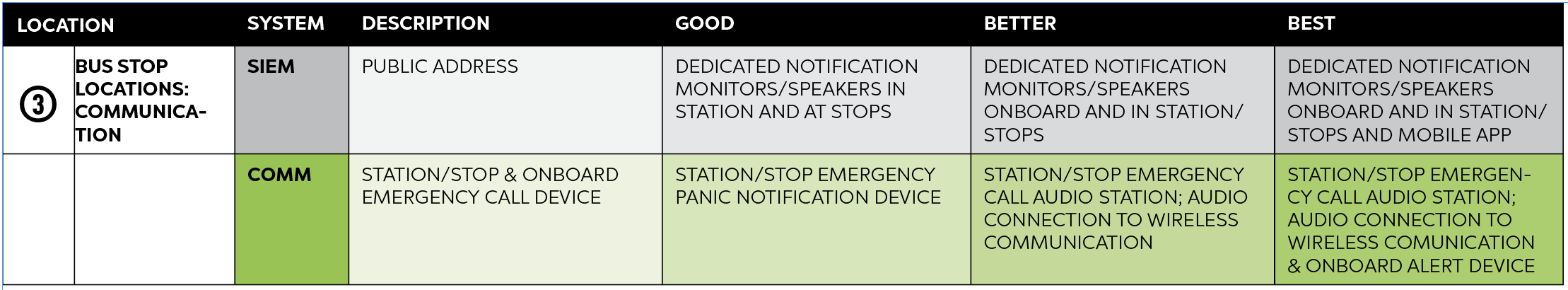
Good, Better and Best system recommendations for bus stop location communications, including specifications for SIEM and communications. To view the guidance with all graphs and charts, please download the full PDF.
④ Bus & Vaulting Areas: Fare Collection
Bus fare collection and vaulting locations, where cash is stored and counted, require reliable security devices to maintain the integrity of revenue collected and the safety of the staff tasked with handling it.
- Sensors to detect passenger fare evasion
- Cash drawer/money clip duress alarms
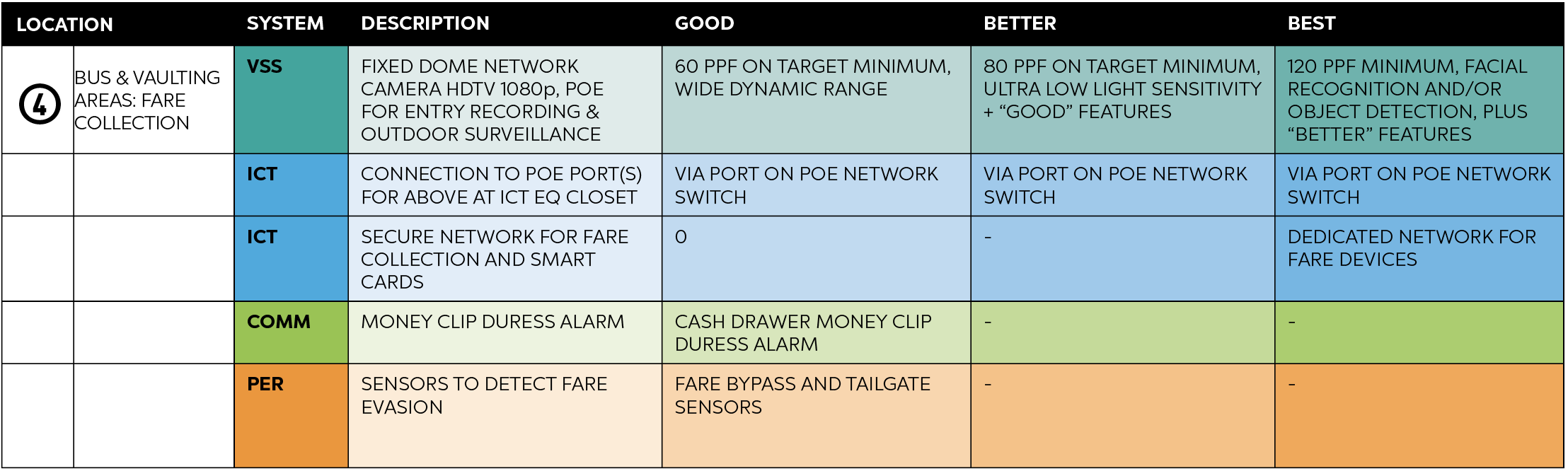
Good, Better and Best system recommendations for bus and vaulting area fare collection, including specifications for video surveillance, ICT, communications and perimeter systems. To view the guidance with all graphs and charts, please download the full PDF.
⑤ Transit Retail
Locations where cash is exchanged, such as transit retail locations and fare vending kiosks housed in robust machines – often located in semi-outdoor spaces without active human monitoring – necessitate specific consideration to maintain public safety during financial transactions.
- Outdoor cameras’ quantity and placement is 60ppf (Good), 80ppf (Better), 120ppf (Best) allowing facial recognition as Best
- Audio and video intercoms are always VoIP compatible and video intercom is video over IP compatible (desktop VoIP station) and mobile device compatible
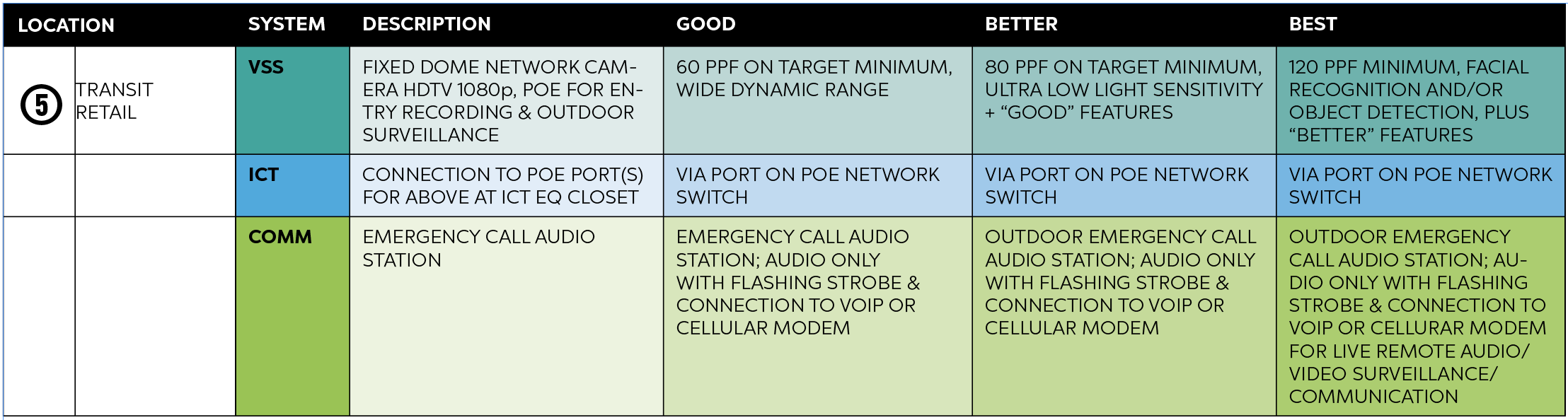
Good, Better and Best system recommendations for transit retail, including specifications for video surveillance, ICT and communications. To view the guidance with all graphs and charts, please download the full PDF.
⑥ Operations Center & Vehicle: Tied Situational Awareness
Situational awareness devices, including vehicle tracking and a multitude of sensors, provide drivers, dispatch and oversight with monitoring systems that not only promote safety but also aid in the proper function of the transit system itself.
- Computer-aided dispatch and automated vehicle location (CAD/AVL)
- Onboard employee notification
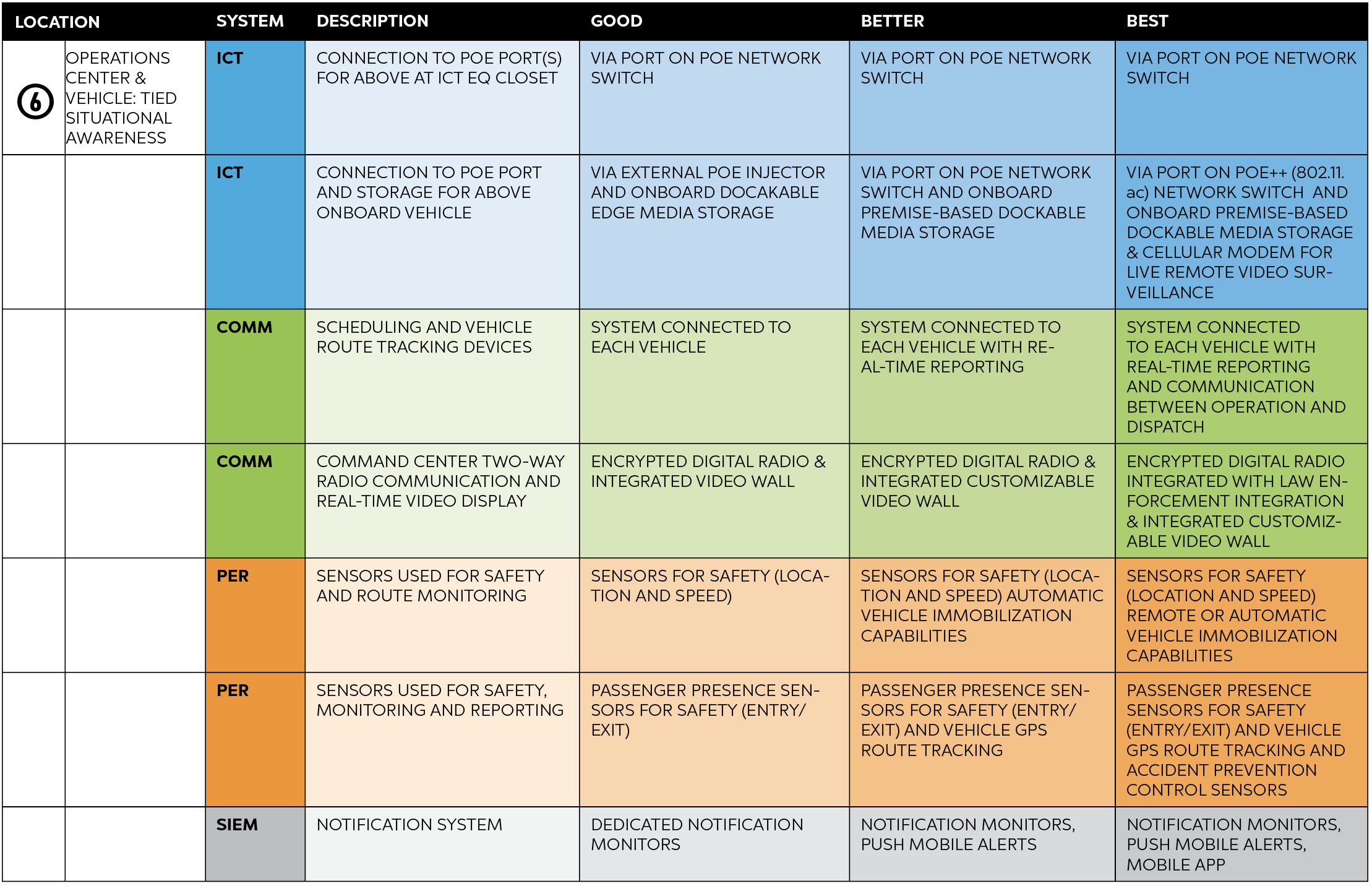
Good, Better and Best system recommendations for operations center and vehicle tied situational awareness, including specifications for ICT, communications, perimeter systems and SIEM. To view the guidance with all graphs and charts, please download the full PDF.
More on G-B-B:
- Good-Better-Best: Comprehensive Best Practices for Implementing Public Transportation Security Systems (Vol. 1)
- Good-Better-Best: A Practical Guide to Implementing a Tiered Offerings Strategy for Customer Choice (for security systems integrators and distributors)
- Good-Better-Best: Comprehensive Best Practices for Implementing Security Systems in Health Care Environments
