Frictionless Access Control: A Look over the Horizon

New uses of biometric and RFID technologies could make access badges obsolete

Henry Hoyne, Northland Controls
The Holy Grail for the global security director is to know who is in the building and to be assured that they belong there. Thus, the nascent drive toward “frictionless access” is seemingly counter-intuitive. The idea is to permit access to an area without interfering with the user’s experience, to make it as natural – as “frictionless” – as possible.
No badge hanging around your neck, no digging in your bag for ID, no presenting credentials to a reader or stopping in front of a camera. Just walk into a controlled space without having to do anything special.
There is an employee recruitment competition at many organizations that comes down to, “My environment is more conducive to your lifestyle than theirs, so you should work here instead of there.” Lanyards, badges, and readers have increasingly entered these organizations’ cross-hairs.
These “stinking badges” get in the way of a free-thinking, free-flowing and collaborative work environment, critics say.

The director who wants to know who is in the building and if they belong there is now being asked to get rid of high-friction badge presentation processes as soon as possible.
Current thinking around frictionless access includes:
- Long-range biometrics. The door is secured, but I can see you coming and will unsecure it before you get to it.
- Short-range radio frequency technology. The door is secured, but I can sense your valid RF device and unsecure the door fast enough for you not to know it.
- Security by exception. Full-time tracking of a wearable device. The door is unsecured until a non-compliant person is sensed, at which time it is automatically secured. The wearable device uses a combination of biometric and RF technology.
Long-Range Biometrics
The most common current approach to long-range biometrics involves facial recognition technology. The simplest deployments use off-the-shelf video cameras with software analytics to reference persons entering the field of view against a database. This works reasonably well at locations with a limited number of people entering and exiting the facility. However, as the population for a given facility or environment goes up, the technology cannot keep up with the required throughput.
If only 25 people need access to a facility, the technology can easily handle this load with a 100 percent success rate. As the number of people goes up to, say, 1,000, though, a success rate even as high as 92 percent becomes unacceptable, since 80 people will either be incorrectly allowed access or incorrectly denied access. In addition, the “friction” created by those failures will create backups, affecting many more people.
More sophisticated technologies use 3D facial modeling. These tend to be significantly more expensive, larger and, potentially, more error-prone. However, extensive research and development are continuing on improving this technology. Considerable work is still needed, though, to achieve the accuracy, reliability, and miniaturization needed for it to be truly effective in high-volume throughput applications.
For high-security areas, facial recognition “who-you-are” technology could be enhanced with voice recognition “what-you-know” codes. Since such areas tend to have relatively low throughput, dual authentication at the entrance would be fairly expedient, though not completely frictionless.
Short-Range Radio Frequency Technology
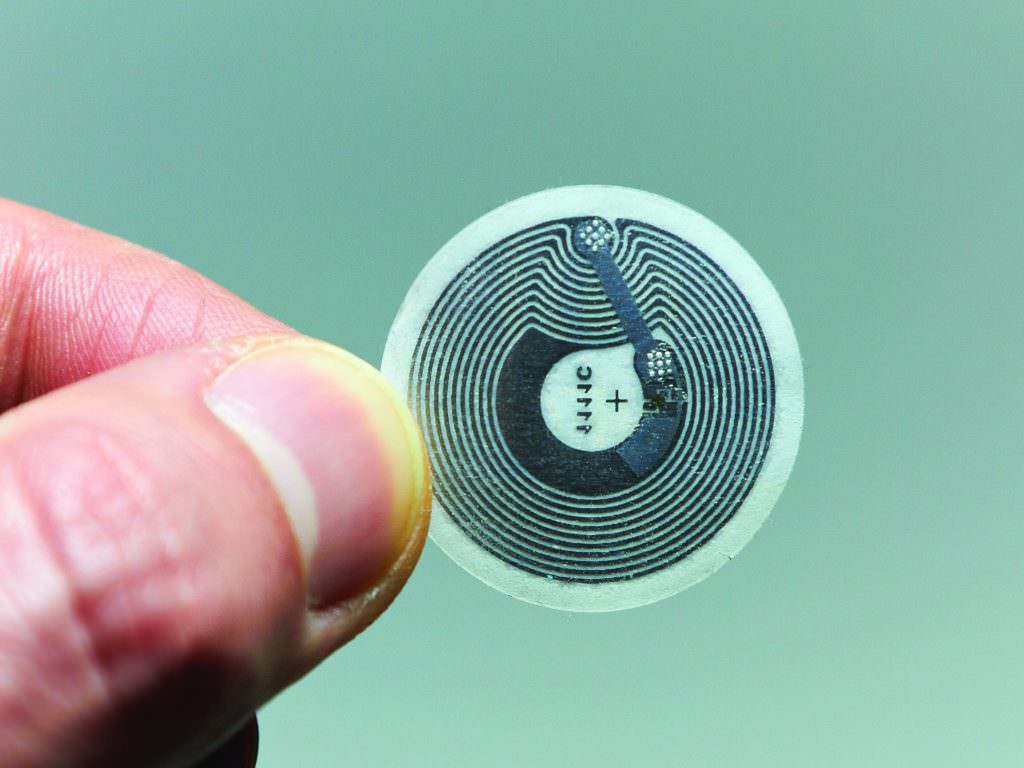
Short-range RF technology is able to identify a person or device carrying either a passive or active RF transmitter. These transmitters can be the size of a quarter or a typical ID badge. When the person or device is in range of a receiver antenna, the system can validate the authorization related to the tag and grant access.
RFID tags have been shown to work well under constrained conditions. However, to increase the accuracy of a system, many more antennas are needed. The antennas usually are only 4×4 inches and can be unobtrusively placed, but the positioning and quantity needed to make the system efficiency can become a maintenance and support issue. Without a wide enough distribution of antennas, it is difficult to determine if a tag is coming or going, whether it is on the other side of a wall, and which access point in a corridor full of access points is the appropriate one to unlock.
Nonetheless, as the sophistication of antennas increases and the correlation with mapping software improves, RFID tags may play an important role in the evolution of frictionless access.
In addition, as smartphones have become ubiquitous, they may simplify the process by transmitting RF signals themselves and making separate tags unnecessary.
Security by Exception
Security by exception combines features of RF technology and biometrics. A smart device would be RF-enabled and would have a real-time view of a biometric feature such as an iris, finger or voice print. An enormous amount of data would be generated, and the system would be able to create a map of every single person in a building, which floor they are on, and what secured areas they are near.
This would go beyond the security director’s dream of knowing who is in the building and being assured that they belong there to also include information about each person’s exact location. Since, in most commercial and industrial settings, people know where they belong and are simply moving around to perform their responsibilities, a majority of controlled access points could simply be unlocked at all times. When the system senses a person who is not authorized for a particular area approaching an access point, it could send a warning and immediately secure the door.
Thus, rather than constantly granting access to people who belong, the system will manage access by exception, locking the door when someone should not be there.
This will be further reinforced through social engineering.
A locked door will suddenly inconvenience a number of people who will immediately become aware that something is amiss, that someone in their midst does not belong. This sudden friction will be unacceptable to staff who have become accustomed to the new paradigm. They will put extraordinary pressure on people who breach areas where they do not belong and discourage them from causing such problems again. They will also put pressure on the security and IT departments that provide and support this new ecosystem. The reliability and accuracy of the system will be paramount.
Individual aspects of the technology needed to make security by exception work exist today. Progress will be made to integrate the technologies and make them faster, smaller and more reliable. As smart devices and “big data” have disrupted how we live our lives today, security by exception will dramatically alter the access control landscape and our awareness of who is in and around secure areas.
Henry Hoyne is vice president of professional services for Northland Controls (www.northlandcontrols.com). He can be reached at hhoyne@northlandcontrols.com.