The Cybersecurity Imperative
A Benchmarking Study of the Cybersecurity Practices and Initiatives of Global Organizations – Produced in partnership with ESI ThoughtLab and WSJ Pro Cybersecurity
Sponsor partners: Security Industry Association (SIA), Baker McKenzie, CyberCube, HP Inc., KnowBe4, Opus, Protiviti and Willis Towers Watson

Supporting Documents, Tools and Resources for SIA Members
Key Finding: Digital transformation is exposing companies to higher and more costly cyber risks.
According to the global benchmarking study, those whose cybersecurity practices do not keep pace with their digital transformation initiatives are more likely to see $1 million or more in losses from cyberattacks.
The research showed that cyber risks rise dramatically as companies embrace new technologies, adopt open platforms and tap ecosystems of partners and suppliers.
“Companies need to make sure that their cybersecurity programs keep pace with their digital transformation effort. Cybersecurity should not be an afterthought. It needs to be integrated into the fabric of an organization’s growth strategy.”
– Lou Celi, CEO of ESI ThoughtLab and director of the study.
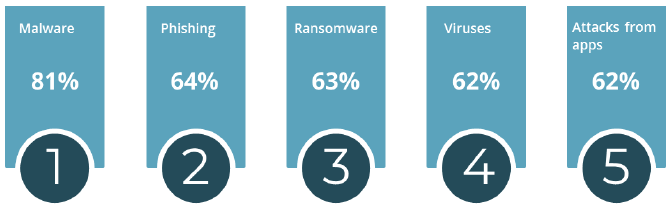
Leading Cyber Threat Vectors in 2018
- Malware (81%)
- Phishing (64%)
- Ransomware (63%)
Expected Increase in Cyber Threat Vectors by 2020
- Attacks through partners, customers and vendors (247% growth)
- Supply chains (+146%)
- Denial of service (+144%)
- Apps (+85%)
- Embedded systems (84%)
Surveyed companies see high risks from external threat actors, such as unsophisticated hackers (cited by 59% of firms), cybercriminals (57%) and social engineers (44%), but the greatest threat lies with untrained general staff (87%). Another 57 percent of firms see data sharing with partners and vendors as their main IT vulnerability. Nonetheless, only 17 percent of companies have made significant progress in training staff and partners on cybersecurity awareness.
Key finding: To win the arms race with hackers, companies are boosting their cybersecurity investments
To cope with rising cyber risks, surveyed companies are increasing their cybersecurity investment by 7 percent this year and 14 percent next year. The biggest upsurge will come from platform companies, which are hiking their spending 59 percent this year and 64 percent next year. On average, companies with revenue between $250 million and #1 billion will spend $2.9 million next year; $1-5 billion ($5.7 million); $5-20 billion ($10.7 million); and $20 billion+ ($16.8 million).
How Companies Allocate Cybersecurity Budgets
- 39.3 percent to technology
- 30.7 percent to process
- 30 percent to people
Companies now use a variety of technologies to improve cybersecurity, such as multi-factor authentication (90%), blockchain (68%), Internet of Things (62%) and artificial intelligence (AI) (44%).
"We are using AI in our access and entitlement management to analyze the behaviors of end-users and determine whether or not their behaviors are risky."
– Ryan Fritts, CISO, ADT
Planned Cybersecurity Investments
Which of the following technologies and IT services to manage cybersecurity risks is your company using now, and which is your company planning to start using over the next two years?
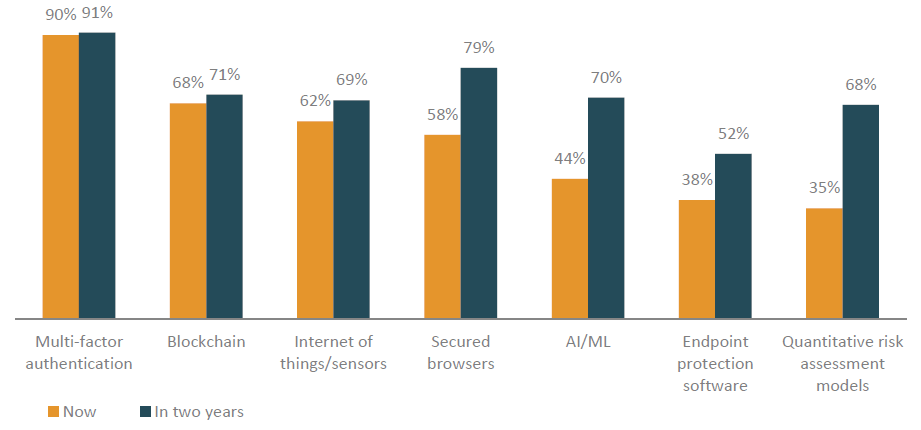
Over the next two years, studied firms indicated they plan to greatly expand the use of the following technology solutions:
- Behavioral analytics (+1,735%)
- Smart grid technologies (+831%)
- Deception technology (+684%)
- Hardware security and resilience (+114%)
Key Finding: Cybersecurity is still a work in progress
 ESI ThoughtLab scored the surveyed companies based on their progress against each area of the National Institute of Standards and Technology's cybersecurity framework, then segmented these firms into three stages of cybersecurity maturity: beginners, intermediates, and leaders. The study’s results reveal that companies have a long way to go with regard to cybersecurity maturity: only 20 percent of companies are leaders, while 31 percent are beginners and 49 percent are intermediates. Interestingly, technology firms have the lowest maturity scores, although platform companies have the highest. Financial services and insurance firms also tend to be further along the maturity curve than average.
ESI ThoughtLab scored the surveyed companies based on their progress against each area of the National Institute of Standards and Technology's cybersecurity framework, then segmented these firms into three stages of cybersecurity maturity: beginners, intermediates, and leaders. The study’s results reveal that companies have a long way to go with regard to cybersecurity maturity: only 20 percent of companies are leaders, while 31 percent are beginners and 49 percent are intermediates. Interestingly, technology firms have the lowest maturity scores, although platform companies have the highest. Financial services and insurance firms also tend to be further along the maturity curve than average.
According to the study, companies have made more progress on risk prevention than resilience. Over the next year, firms will continue to allocate the largest share of their investment to protection (26.5%), but will allocate more to respond (19.2%) and recover (18.1%) to increase resilience as attacks rise.
Nations with Highest Cybersecurity Maturity Scores
- U.S. (107.2)
- South Korea (104.7)
- Japan (102.6)
- France (101.9)
- Australia (101.3).
Most of the lowest scoring companies were headquartered in emerging markets, including Brazil (88.6), Argentina (93.6) and India (93.7), although companies in Germany (97.3) and Switzerland (96.3) also had relatively low scores.
Key Finding: The returns on cybersecurity maturity
The study shows that as corporate cybersecurity systems mature, the probability of costly cyberattacks declines. Cybersecurity beginners have a 21.1-percent probability of cyberattacks generating over $1 million in losses versus 16.1 percent for intermediates and 15.6 percent for leaders. The costs of cyberattacks also decrease as cybersecurity matures: the costs for beginners is 0.039 percent of revenue ($3.9 million for a $10-billion company) compared with 0.012 percent of revenue for leaders ($1.2 million for a $10-billion company). However, these costs and the number of successful attacks are harder to measure for beginners due to their inadequate detection systems.
Percentage of Firms by Cybersecurity Stage
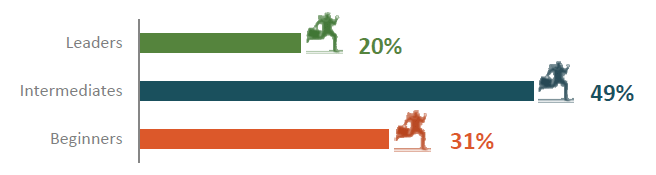
Cybersecurity beginners have a 21.1-percent probability of cyberattacks generating over $1 million in losses vs 16.1 percent for intermediates, and 15.6 percent for leaders.
Despite better monitoring methods and metrics, most companies still do not know the return on investment of their cybersecurity investments. One stumbling block is that firms often do not measure indirect costs, such as productivity loss, reputational damage and opportunity costs, which can hurt bottom lines. Another is the difficulty of gauging risk probabilities and the failure to take into account the upside from improving productivity (cited by 35 percent of companies), profitability (22%), corporate reputations (18%), competitive positioning (16.2%) and customer engagement (11%).
Call to Action: Don't Manage Cyber and Physical Security in Silos
"Security is a holistic discipline. You need to manage both physical and cyber risks. You could have the best physical security ever – guards, gates, guns and surveillance – but if someone can access your network from the comfort of their living room, it's not doing anything. The reverse is true as well. You could have a ton of cybersecurity but fail to lock down your physical space."
– Joseph Gittens, SIA Director of Standards, and Cybersecurity Imperative study advisor