The Risk of AI Shadow Data

Storing video data used to simply involve storing the video from the camera and another basic event database of motion events or other basic yes/no triggers. With all of the metadata created by some cameras now, however, it is also necessary to store this additional data somewhere. System designers need to take this data into account, from transmission across the network to VMS processing and storing to the ability to quickly pull it when searching for an event. Failing to do so can lead to lost data or very slow systems that may time out before the data can be retrieved.
It is also necessary to understand where your data resides. This can be local, in the “cloud” or in some type of hybrid model. When designing a system, or searching for one that fit your needs, ensure that the vendor can clearly explain this. It may be necessary to check your organization’s regulations on collecting and storing data. Improper storage could put your organization at risk. Consider reviewing ISO 42001, which is the standard for artificial intelligence (AI) management systems.
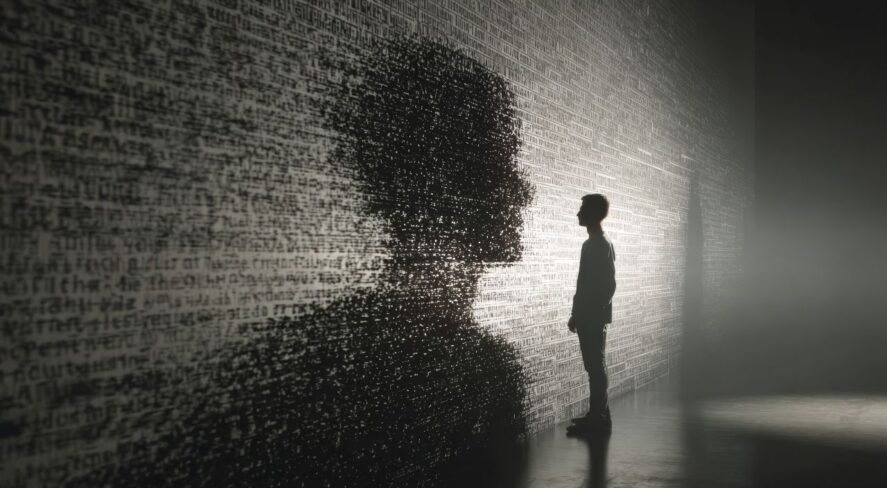
Once a user finds an event and exports the data, there is a new risk—shadow data. Without a policy to manage where exported data resides and who manages it, there could potentially be a copy of that data that is at risk of being lost. This data might not be encrypted or protected and could fall into the wrong hands. Most platforms have safeguards against this, such as password-protected exports or proprietary viewers, but these are only as effective as strong internal policies.
To summarize, it is important to design your AI-enhanced security system to handle the additional data that wasn’t there just a few years ago. Ensure that you and your company understand where your data resides and how this relates to regulatory compliance. And have a policy for handling exported data to ensure that it remains secure.
The views and opinions expressed in guest posts and/or profiles are those of the authors or sources and do not necessarily reflect the official policy or position of the Security Industry Association.
This article originally appeared in All Things AI, a newsletter presented by the SIA AI Advisory Board.
